- / Title
Post-Quantum Cryptography and Secure Computing Applications Titles | phdassistance.com
Info: 1557 words(1 pages) Post-Quantum Cryptography and Secure Computing Applications Titles | phdassistance.com
Published: 28th April 2026 in Post-Quantum Cryptography and Secure Computing Applications Titles | phdassistance.com
Share this:
Related Services
Introduction
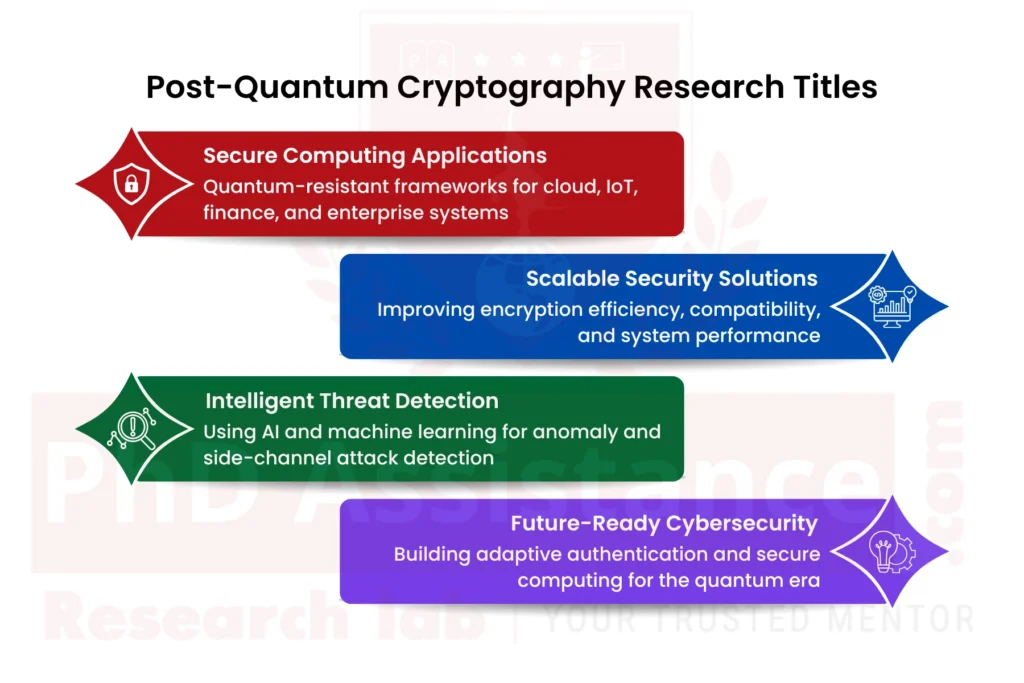
Cybersecurity researchers expand their research scope because they struggle to discover new PhD research topics that need to be investigated for their present academic value. PhD Assistance provides expert guidance in doctoral research area selection, which ensures academic originality, technical value and publication potential. Our team in Post-Quantum Cryptography for Secure Computing Systems helps researchers select their research areas by presenting them with research options that include quantum-resistant encryption and secure cloud platforms, IoT security and authentication models and financial cybersecurity. Our experts ensure each topic aligns with current security challenges, university standards, and industry needs. The researchers use our selection assistance to identify their research topics, which enables them to finish their doctoral studies while making significant academic contributions.
Proposed PhD Title 1: Developing a Scalable Post-Quantum Cryptography Framework for Secure Cloud Data Protection Using Hybrid Lattice-Based Algorithms
Post-Quantum Cryptography (PQC) has become one of the most important research areas in modern cybersecurity because quantum computers will use their advanced capabilities to break all traditional encryption systems, which depend on RSA and Elliptic Curve Cryptography (ECC) for security. Secure encryption systems are essential because cloud computing environments handle massive amounts of personal data, financial information and healthcare records, and enterprise data, which needs protection. Cloud systems require cryptographic systems that deliver strong security protection while supporting their processing requirements and maintaining their capacity to connect with distributed networks. Hanafi and Ali (2025) demonstrated that PQC algorithms face practical implementation challenges because they have efficiency problems that require excessive keys to operate successfully.
Problem Statement:
The current Post-Quantum Cryptography in Cybersecurity algorithms face multiple challenges because they require large key sizes, their operations consume extra bandwidth, their processing capabilities fall short of actual operational requirements, and their implementation in cloud systems faces major obstacles. The system performance decreases because these restrictions create extra storage and processing requirements, which make it difficult to use cloud applications that need real-time operations. The transition from traditional encryption systems to post-quantum systems creates compatibility challenges, which make it harder for organisations to implement secure post-quantum systems throughout their large operational areas.
Research Gap:
The present research material provides research studies about pure research hybrid PQC frameworks, which achieve quantum security together with their ability to process data, use storage space, and operate in cloud environments.
Research Question:
How can hybrid lattice-based PQC algorithms improve secure, scalable, and efficient cloud data protection against future quantum attacks?
Outcome:
The research will develop a cloud security framework that protects distributed data assets through enhanced encryption efficiency while enabling organisations to implement PQC technologies in their cloud systems.
Reference:
Hanafi, B., Ali, M. Analyzing the research impact in post quantum cryptography through scientometric evaluation. Discov Computing 28, 32 (2025). https://doi.org/10.1007/s10791-025-09507-3 .
Proposed PhD Title 2. Designing Lightweight Post-Quantum Cryptographic Protocols for Secure IoT Networks in Resource-Constrained Environments
The Internet of Things (IoT) technologies have grown rapidly, which has changed how various industries function in healthcare, manufacturing, transportation, agricultural operations and smart city development. The IO devices create a need for secure communication because they transmit confidential data through their interconnected networks. The traditional cryptographic methods face two main threats because they cannot withstand future quantum attacks and because most Post-Quantum Algorithms need excessive memory, energy and processing power that IoT devices cannot support. Hanafi and Ali (2025) identified the lack of efficient PQC implementation in constrained environments as a major research challenge. Future development of Internet of Things ecosystems requires the creation of lightweight Quantum-Resistant Encryption Techniques which provide security while enabling battery life, bandwidth preservation and low-latency communication.
Problem Statement:
Low-power Internet of Things devices, with their restricted memory, battery life and processing capacity requirements, cannot use existing post-quantum algorithms because those algorithms need too much computational power. The system suffers from performance issues because its cryptographic operations require too many resources, which leads to increased latency, decreased device performance and shorter operational time. Most connected devices lack protection against future quantum security threats because there is no effective, lightweight security solution.
Research Gap:
Researchers have conducted insufficient studies to create lightweight PQC communication protocols that specifically address energy efficiency and memory limits, and real-time operational requirements of IoT environments.
Research Question:
How can lightweight PQC protocols improve secure communication, energy efficiency, and scalability in IoT networks?
Outcome:
The research will develop an IoT-compatible PQC protocol that reduces processing needs and improves device protection while supporting practical applications in smart connected networks.
Reference:
Hanafi, B., Ali, M. Analyzing the research impact in post quantum cryptography through scientometric evaluation. Discov Computing 28, 32 (2025). https://doi.org/10.1007/s10791-025-09507-3
Proposed PhD Title 3. Building Adaptive Post-Quantum Authentication Models for Cross-Platform Cybersecurity Systems
Current digital organisations need to operate multiple platforms, which encompass their cloud systems and their enterprise servers, their mobile devices, their edge computing environments and their web applications. Authentication systems function as essential components that safeguard access to protected information and online services. The authentication methods that use classical cryptography face potential security risks because of upcoming quantum technology. Hanafi and Ali (2025) identified cross-platform adaptability as one of the major unresolved issues in Secure Computing in the Post-Quantum Era. Future cybersecurity systems need authentication systems that can adapt to diverse operational contexts while maintaining identical security standards.
Problem Statement:
Current authentication systems do not provide cross-platform authentication methods that remain secure against quantum attacks from cloud environments, mobile devices, enterprise systems, and edge computing environments. Organisations depend on separate identity systems, which create problems with system compatibility, slow down access control and lead to different security standards. The existing weaknesses of authentication systems will become more severe when quantum computing makes classical authentication methods obsolete.
Research Gap:
The current system requires an adaptive PQC authentication system that enables secure cross-platform authentication while maintaining system performance and user experience.
Research Question:
How can adaptive PQC authentication models enhance cybersecurity across cloud, mobile, enterprise, and edge computing systems?
Outcome:
The research project will create an authentication framework that provides flexible identity verification protection for digital systems used across multiple platforms..
Reference:
Hanafi, B., Ali, M. Analysing the research impact in post quantum cryptography through scientometric evaluation. Discov Computing 28, 32 (2025). https://doi.org/10.1007/s10791-025-09507-3
Proposed PhD Title 4. Developing Machine Learning-Based Side-Channel Attack Detection for Post-Quantum Cryptographic Hardware Systems
Theoretical designs of PQC algorithms require their implementation security to protect their hardware designs, which they use in actual operational environments. Embedded systems, secure processors, mobile devices, and smart cards continue to face potential side-channel attacks through power consumption analysis and electromagnetic leakage, timing attacks and thermal signature analysis. The attacks enable attackers to obtain secret keys while keeping the fundamental algorithm intact. Hanafi and Ali (2025) demonstrated that Post-Quantum Cryptography Algorithms need better protection mechanisms to defend against hardware attacks that target Cybersecurity systems. Machine learning provides a promising solution by identifying abnormal patterns and suspicious leakage signals in real time.
Problem Statement:
Current authentication systems use Slack cross-platform authentication methods, which maintain security against quantum attacks that originate from cloud environments, mobile devices, enterprise systems and edge computing environments. Multiple identity systems create access control delays and security standard variations, which lead to system compatibility problems for organisations. Authentication systems face their current weaknesses, which will worsen through quantum computing because it will render classical authentication methods useless.
Research Gap:
The existing research on integrated intelligent systems has not developed successful systems that use machine learning to monitor real-time side-channel threats in PQC hardware environments.
Research Question:
How can machine learning improve side-channel attack detection and hardware security in post-quantum cryptographic systems?
Outcome:
The research will develop an intelligent monitoring system that will improve PQC protection through hardware security and its ability to detect anomalies and support secure operations of embedded systems.
Reference:
Hanafi, B., Ali, M. Analyzing the research impact in post quantum cryptography through scientometric evaluation. Discov Computing 28, 32 (2025). https://doi.org/10.1007/s10791-025-09507-3
Proposed PhD Title 5. Creating a High-Performance Hybrid Post-Quantum Encryption Architecture for Secure Financial Transactions
The sectors of digital banking, e-commerce, online payments, blockchain finance and cross-border transaction systems need strong encryption and secure authentication methods. The financial security systems that use RSA and ECC traditional models will become insecure when quantum computing technology reaches operational capacity. Financial systems need encryption systems that can process transactions quickly while meeting regulatory standards, protecting customer information, and maintaining security for extended periods. The authors Hanafi and Ali (2025) demonstrated that practical PQC systems need to be implemented across various real-world sectors. Financial institutions entering the quantum era will find it easier to transition through Hybrid models that Lattice-Based Cryptography Applications support.
Problem Statement:
The modern PQC methods will slow down transactions because these methods require more processing power and create compatibility issues between fast, secure processing systems of financial institutions. Financial institutions need encryption methods that operate with minimal delay to handle their multiple daily transactions, but most PQC algorithms create performance hindrances. The development of secure quantum-resistant financial systems requires hybrid solutions that need to be optimised for successful migration to these systems.
Research Gap:
There is not enough research about hybrid PQC architectures that achieve high performance while providing a secure and scalable solution for conducting efficient financial transactions.
Research Question:
How can hybrid PQC architectures improve security, compatibility, and transaction efficiency in digital financial systems?
Outcome:
The research will develop a financial encryption framework that protects future banking systems, payment services, and quantum-based financial operations with secure and efficient security measures.
Reference:
Hanafi, B., Ali, M. Analyzing the research impact in post quantum cryptography through scientometric evaluation. Discov Computing 28, 32 (2025). https://doi.org/10.1007/s10791-025-09507-3 .
Need assistance finalising your dissertation topic? Selecting a strong, researchable topic can be challenging — but you don’t have to do it alone.
Our research consultants can help refine your ideas, identify literature gaps, and guide you toward a topic that aligns with current academic trends and your programme requirements.
Contact us to begin one-on-one topic development and refinement with PhdAssistance.com Research Lab.
Share this:
Cite this work
PhDAssistance. (n.d.). Virtual Influencers Dissertation Titles Retrieved 30th January 2026, from https://www.phdassistance.com/title/virtual-influencers/
“Virtual Influencers Dissertation Titles, https://www.phdassistance.com/title/virtual-influencers/
“Virtual Influencers Dissertation Titles” PhDAssistance, PhDAssistance, Tuesday, January 30th,2026.
PhDAssistance, n.d. Virtual Influencers Dissertation Titles[Online]. Available at: https://www.phdassistance.com/title/virtual-influencers/ [Accessed January 30th, 2026].
PhDAssistance. Virtual Influencers Dissertation Titles[Internet]. PhDAssistance; [cited 2026 January 30th]. Available from: https://www.phdassistance.com/title/virtual-influencers/
PhDAssistance (n.d.).
Virtual Influencers Dissertation Titles. Retrieved January 30th, 2026, from https://www.phdassistance.com/title/virtual-influencers/
PhDAssistance, Virtual Influencers Dissertation Titles(PhDAssistance, n.d. January 30th accessed 2026.
Study Resources
Free resources to assist you with your university studies!
